Exabeam Releases Security Intelligence Platform for Early Detection of Ransomware
Thursday, June 16, 2016

|
Richard Harris |
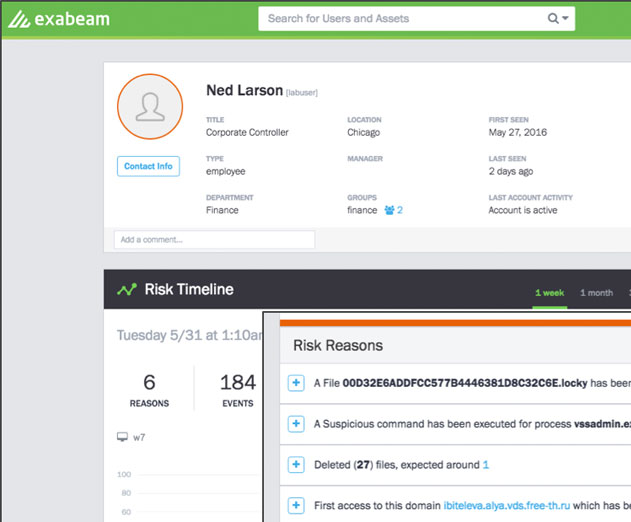
Exabeam has released Exabeam Analytics for Ransomware, a new behavior-based security intelligence platform designed for early detection of ransomware across a corporate network. Exabeam can detect ransomware movement and activity in the network, the servers, workstations, BYOD devices, and cloud services.
Exabeam detects ransomware as it first enters the network and begins to spread. It uses both behavioral analysis and file analysis for:
- Detecting new (unknown) ransomware via machine-learning: With no signatures and no static correlation rules, Exabeam learns the normal file and document behaviors of an organization’s employees, and quickly finds the anomalies associated with ransomware infection.
- Detecting known ransomware via indicators of compromise: Known ransomware processes use certain file extensions and have known patterns or other indicators listed in threat intelligence feeds. The Exabeam Threat Research Team verifies these indicators and implements them in the product.
- Infrastructure-wide, hybrid-cloud ransomware protection: By looking at machine logs, Exabeam can detect ransomware operating on endpoints, in the datacenter or against cloud based storage services. For example, an employee might access corporate files on the cloud sharing service Box from home, using his personal device, and in the process, allow ransomware to begin encrypting the Box files. Other employees accessing the same corporate files enable the malware to infect their corporate workstations and begin moving across the corporate network. Exabeam can detect this activity end to end, and early enough to prevent disruption.
Exabeam Analytics for Ransomware can inter-operate with specific security technologies, such as endpoint protection products, to perform additional analytics. It is available as either a physical appliance or a virtual machine. Pricing is based on number of users.
Read more: http://www.exabeam.com/product/applications

Become a subscriber of App Developer Magazine for just $5.99 a month and take advantage of all these perks.
MEMBERS GET ACCESS TO
- - Exclusive content from leaders in the industry
- - Q&A articles from industry leaders
- - Tips and tricks from the most successful developers weekly
- - Monthly issues, including all 90+ back-issues since 2012
- - Event discounts and early-bird signups
- - Gain insight from top achievers in the app store
- - Learn what tools to use, what SDK's to use, and more
Subscribe here



_cptybzmh.jpg)








