New Study by University of Cambridge Show 87 Percent of Android Devices Vulnerable
Tuesday, October 20, 2015

|
Richard Harris |
A new study by researchers at the University of Cambridge and published by AndroidVulnerabilities.org shows that 87% of Android devices are vulnerable to attack by malicious apps and messages.
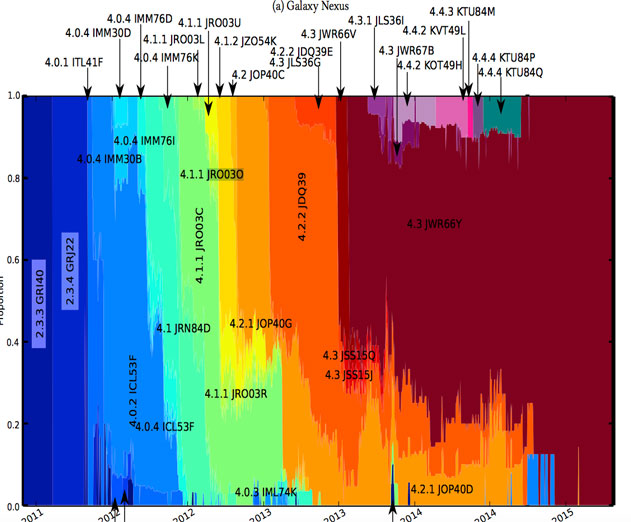
The study suggests that the reason for this high vulnerability rate is in part due to the fact that device manufacturers are not providing regular security updates. The researchers say that some manufacturers are much better than others in providing security updates and devices built by LG and Motorola, as well as those devices shipped under the Google Nexus brand, are better providing regular security updates than most.
The study uses data collected by the University of Cambridge’s Device Analyzer app, which is available from the Google Play Store.
Study Abstract:
In the paper the authors map the complex network of players in the Android ecosystem who must collaborate to provide updates, and determine that inaction by some manufacturers and network operators means many handsets are vulnerable to critical vulnerabilities. They define the FUM* security metric to rank the performance of device manufacturers and network operators, based on their provision of updates and exposure to critical vulnerabilities.
Using a corpus of 20,400 devices they show that there is significant variability in the timely delivery of security updates across different device manufacturers and network operators. This provides a comparison point for purchasers and regulators to determine which device manufacturers and network operators provide security updates and which do not. They found that on average 87.7% of Android devices are exposed to at least one of 11 known critical vulnerabilities and, across the ecosystem as a whole, assign a FUM security score of 2.87 out of 10. In the data, Nexus devices do considerably better than average with a score of 5.17; and LG is the best manufacturer with a score of 3.97.
*The FUM security score was developed by AndroidVulnerabilities.org and represents the following:
F - The proportion of devices free from known critical vulnerabilities.
U - The proportion of devices updated to the most recent version.
M - The number of vulnerabilities the manufacturer has not yet fixed on any device.
Read more: https://www.cl.cam.ac.uk/~drt24/papers/spsm-scorin...

Become a subscriber of App Developer Magazine for just $5.99 a month and take advantage of all these perks.
MEMBERS GET ACCESS TO
- - Exclusive content from leaders in the industry
- - Q&A articles from industry leaders
- - Tips and tricks from the most successful developers weekly
- - Monthly issues, including all 90+ back-issues since 2012
- - Event discounts and early-bird signups
- - Gain insight from top achievers in the app store
- - Learn what tools to use, what SDK's to use, and more
Subscribe here